3 January 2026
Recently, the french edition of Tom's Hardware, the leading destination for tech enthusiasts of all skill levels, has compared features, perfomance, price and speed of the major VPNs in France. Tom's Hardware compared 20 VPNs including Trust.Zone.
TrustZone was chosen as the best VPN that offers the best monthly price / confidentiality in France.
Besides that, Trust.Zone is selected in top 3 cheapest providers in France according to Tom's Hardware. read more...
1 January 2026
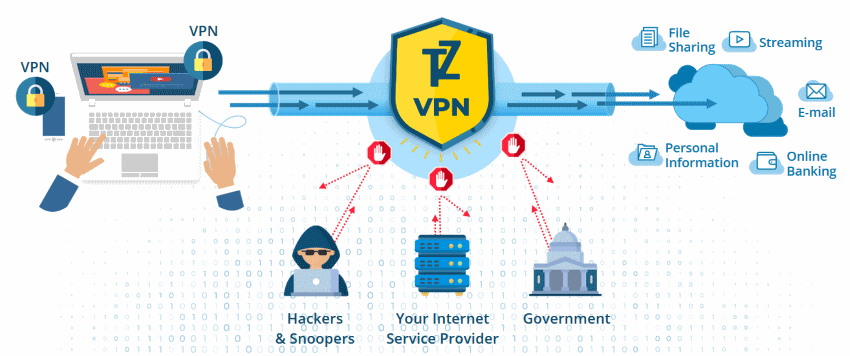
Today we have instant access to mobile banking, digital payments, investment apps, and blockchain transactions. However, security risks also grow. More than 90% of breaches in 2024 had financial reasons. The fintech industry handles sensitive data, the main target of cybercriminals. A data leak means millions of dollars in losses, fines, and serious reputational damage.
How to stay protected?
Implement strong digital defenses. Usually, companies use several layers of protection, and one of them is VPN. Earlier, it was used as an optional solution for privacy, but now VPN is a must-have component of a security system. How exactly does a VPN work and protect data? Let’s have a closer look! read more...
1 January 2026
VPN ensures that the users can work on a private network and not have a fear of compromise. But beyond just protecting your privacy on the internet, there are other ways to maximize your VPN.
Here are 9 ways to optimize your VPN use. read more...
5 December 2025
We’re excited to share that Trust.Zone VPN now supports the VLESS protocol!
VLESS is a lightweight, next-generation VPN protocol designed to provide faster, more secure, and more efficient connections.
Unlike older protocols, VLESS minimizes data overhead, adapts easily to unstable networks, and is great at bypassing censorship. It’s flexible, encryption-agnostic, and perfect for activities like gaming, streaming, and secure browsing—offering a seamless balance between speed and privacy.
Let’s explore why VLESS is a great upgrade for your VPN experience. read more...
3 December 2025
RestorePrivacy, the leading service, providing users with useful privacy and security information, has recently ranked TrustZone among Top 3 Free Trial VPNs
According to RestorePrivacy, everything published on this site is honest, free of charge, and open to everyone. Nothing is locked behind a paid membership wall. read more...
28 November 2025
New reviews of Trust.Zone VPN service are appearing on the web! We have created a list of the most significant reviews of Trust.Zone VPN during the last week - from CNET, VPNFan and other tech websites.
What’s a Trust.Zone VPN, what are the best advantages and features of Trust.Zone VPN - read the opinions of the most popular tech blogs on the web! read more...
4 November 2025
President Trump is reportedly finalizing an executive order that would force major tech firms to embed law-enforcement backdoors into consumer-grade encryption tools. The draft would require companies to provide decryption keys to authorized agencies on demand, eroding the safeguards that protect private messages and stored data.
It also calls for unprecedented cross-agency data sharing, mandating “unfettered access” to unclassified records held by state and local programs.
Privacy experts warn this could weaken online security and prompt a renewed surge in VPN use, much like the spike seen after the recent TikTok ban. read more...
17 October 2025
Need an EXTRA discount for Trust.Zone VPN? It's easy.
Pay with Bitcoin or other crypto and automatically get additional 10% OFF.
Why Bitcoin? Bitcoin is the most anonymous and safe payment method. No personal details needed! Lastname, firstname, credit card details are NOT NEEDED! The limited time offer. read more...
10 October 2025
RestorePrivacy, the leading service, providing users with useful privacy and security information, has recently ranked TrustZone as the Best Free Trial VPN among 300+ VPNs worldwide.
Whether you decide to go with one of the short-term free trial VPN services or a risk-free 30-day trial VPN service, both options will allow you to test out the VPN without any risk. read more...
10 October 2025
Big news for Mac users — Trust.Zone just launched its first-ever native VPN app for macOS!
Built from scratch for Apple devices, this version brings some serious power under the hood and is ready to take your online privacy to the next level.
Give it a try and let us know what you think! read more...