<< Todos los mensajes1 febrero 2026
Indiana is trying a new way to control access to online porn. State officials say that porn websites should block users who visit through VPNs. According to them, this would help enforce age-verification laws and stop minors from seeing adult content.
Indiana already has a law that requires porn websites to check that users are over 18. In many cases, this means asking people to upload an ID or use a third-party verification service. The state argues that VPNs make these checks useless, because VPNs hide a user’s real location.
In simple terms, Indiana believes that if porn sites allow VPN traffic, they are helping people avoid the law. leer más...
3 diciembre 2025
RestorePrivacy, the leading service, providing users with useful privacy and security information, has recently ranked TrustZone among Top 3 Free Trial VPNs
According to RestorePrivacy, everything published on this site is honest, free of charge, and open to everyone. Nothing is locked behind a paid membership wall. leer más...
4 noviembre 2025
President Trump is reportedly finalizing an executive order that would force major tech firms to embed law-enforcement backdoors into consumer-grade encryption tools. The draft would require companies to provide decryption keys to authorized agencies on demand, eroding the safeguards that protect private messages and stored data.
It also calls for unprecedented cross-agency data sharing, mandating “unfettered access” to unclassified records held by state and local programs.
Privacy experts warn this could weaken online security and prompt a renewed surge in VPN use, much like the spike seen after the recent TikTok ban. leer más...
30 septiembre 2025
Journalists exposing a North Korean cyberattack saw their Proton accounts suspended without warning. For a service that calls itself “logless,” this is a shocking move.
Our new article uncovers what really happened and why it matters for anyone relying on privacy tools.
Learn why Trust.Zone offers the anonymity and consistency others fail to deliver. leer más...
1 julio 2025
The rate at which folks visit adult websites is on the upward trajectory, and the trends show no signs of stopping any time soon. According to report, adult websites are more popular than Amazon and Netflix. But here’s the point: as much watching adult content is often discussed in a morality context, a huge elephant in the house is usually overlooked – security and privacy.
If you think that you will never be affected by such issues, this could be the right time to reconsider. leer más...
29 junio 2025
The demand for VPN services in Florida skyrocketed by over 1,000% after Pornhub blocked access in response to a new age verification law. This dramatic increase highlights how users are turning to VPNs to bypass regional restrictions and maintain access to online content.
With Florida users rushing to regain access, Trust.Zone VPN quickly responded by adding more bandwidth and deploying additional servers in Florida to maintain fast and reliable connections.
Many users rely on VPNs for various private purposes, ensuring their online activities remain anonymous and secure. Thankfully, Trust.Zone VPN operates under a strict no-logs policy, meaning that user activities are never recorded or stored. This guarantees that all website visits and online interactions remain completely private and untraceable, giving users peace of mind while browsing the web. leer más...
6 febrero 2025
As concerns over TikTok's data privacy have led users to seek alternatives, many have turned to RedNote, a Chinese social media app known as Xiaohongshu. However, recent analyses reveal that RedNote may not offer the privacy safeguards users are seeking.
Lets look at 5 hidden dangers of RedNote according to privacy experts leer más...
6 febrero 2025
DeepSeek AI, a rapidly emerging Chinese artificial intelligence platform, has been recently at the center of multiple security incidents and growing scrutiny from international authorities. These developments have raised significant concerns about the platform's data handling practices and overall safety.
In response to these security concerns, several governments and organizations have taken precautionary measures.
If you decide to use DeepSeek AI despite its security concerns, using a trusted VPN is highly recommended to safeguard your privacy leer más...
3 enero 2025
The moment you connected your computer to the Internet, you placed it on the 'cyber' battlefield. You might not want to fight in a cyber war, you probably just want to browse the web and check Facebook in peace, but simply by connecting your computer to the Internet, you have placed it, and everything on it, 'in harm's way'.
Would you send a soldier off to battle without body armor? No, so don't send your computer out into the fray unprotected. The enemy doesn't care what country you claim as your own, they don't care that behind the screen is a 65 year-old grandmother who loves to knit sweaters and watch funny cat videos.
So ask yourself the question: Is my computer ready for battle? leer más...
17 octubre 2024
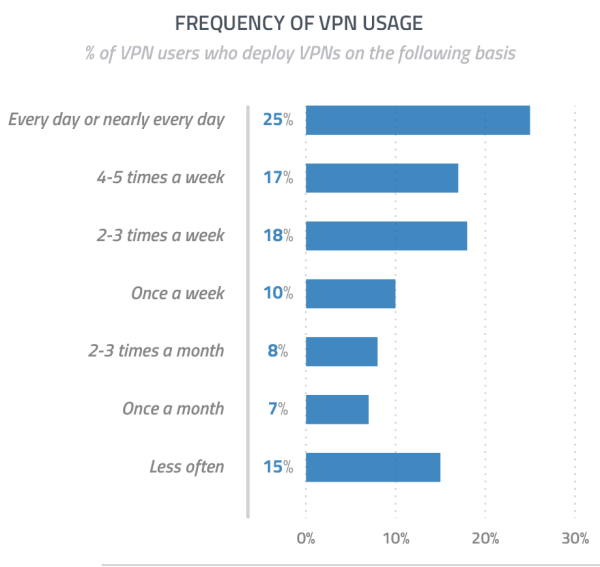
1 in 4 VPN users accessing daily – according to new report by GlobalWebIndex. The main question of the survey was “How frequently do you use VPNs to connect the Internet?
At least, 10% of VPN users access VPN once a week. 7% - once a month. Report was presented by GlobalWebIndex Web Analytics Company. leer más...