<< Alle Beiträge1 Januar 2026
Today we have instant access to mobile banking, digital payments, investment apps, and blockchain transactions. However, security risks also grow. More than 90% of breaches in 2024 had financial reasons. The fintech industry handles sensitive data, the main target of cybercriminals. A data leak means millions of dollars in losses, fines, and serious reputational damage.
How to stay protected?
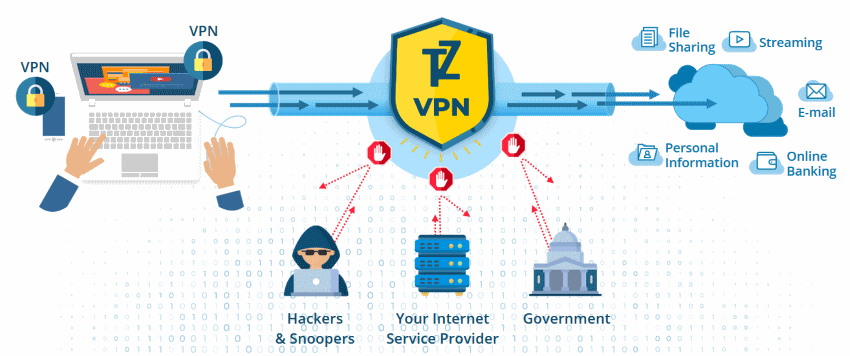
Implement strong digital defenses. Usually, companies use several layers of protection, and one of them is VPN. Earlier, it was used as an optional solution for privacy, but now VPN is a must-have component of a security system. How exactly does a VPN work and protect data? Let’s have a closer look! weiterlesen...
1 Januar 2026
VPN ensures that the users can work on a private network and not have a fear of compromise. But beyond just protecting your privacy on the internet, there are other ways to maximize your VPN.
Here are 9 ways to optimize your VPN use. weiterlesen...
4 November 2025
President Trump is reportedly finalizing an executive order that would force major tech firms to embed law-enforcement backdoors into consumer-grade encryption tools. The draft would require companies to provide decryption keys to authorized agencies on demand, eroding the safeguards that protect private messages and stored data.
It also calls for unprecedented cross-agency data sharing, mandating “unfettered access” to unclassified records held by state and local programs.
Privacy experts warn this could weaken online security and prompt a renewed surge in VPN use, much like the spike seen after the recent TikTok ban. weiterlesen...
1 Oktober 2025
With technology – smartphones, tablets, laptops, etc. – being used more and more worldwide, it’s no wonder there are many more public and guest Wi-Fi hotspots than in previous years.
But, with more convenient Wi-Fi hotspots there are possible security risks, where personal information can be stolen and exposed without you knowing it. Without adequate protection, you’ll risk exposing your online identity and money to online hacks.
With that said, here are 8 effective ways to stay safe, should you plan to use public Wi-Fi. weiterlesen...
11 April 2025
Data breach is a term that everyone using the internet knows these days. And some people are very casual about it. Well, basically the problem is, you do not know the depths of the water until you start drowning.
So, before it is too late start learning to swim. What we are trying to tell you here is that sharing your data with Facebook, Google is another thing but allowing security threats and making your computer or gadgets prone to hackers is another thing.
So here are some internet security facts that everyone should know while they are accessing the internet. weiterlesen...
21 März 2025
Using a VPN for your home network is a great idea, but business leaders should understand the importance of having a VPN for their corporate network. Now that more and more people are working remotely and that companies are managing network access on numerous fronts, one of the best ways to keep your employees safe online is with a VPN.
But that doesn’t mean that a VPN can’t be exploited, nor does it mean that you shouldn’t complement it with other cybersecurity solutions. After all, a VPN can help you dispel some common cybersecurity myths, while additional security protocols can help keep your VPN network completely secure.
Let’s take a look at what these are and what you can do to prevent your VPN from getting hacked. weiterlesen...
3 Januar 2025
The moment you connected your computer to the Internet, you placed it on the 'cyber' battlefield. You might not want to fight in a cyber war, you probably just want to browse the web and check Facebook in peace, but simply by connecting your computer to the Internet, you have placed it, and everything on it, 'in harm's way'.
Would you send a soldier off to battle without body armor? No, so don't send your computer out into the fray unprotected. The enemy doesn't care what country you claim as your own, they don't care that behind the screen is a 65 year-old grandmother who loves to knit sweaters and watch funny cat videos.
So ask yourself the question: Is my computer ready for battle? weiterlesen...
6 Juni 2024
It's a tough reality, but cyber attacks aren't letting up any time soon.
You’ll learn some cybersecurity challenges to expect in 2025 and how you can keep yourself protected.
Here are top 4 cybersecurity challenges in 2025 - 5G security concerns, AI and Machine Learning attacks, IoT security challenges, Social engineering (phishing and etc) weiterlesen...
30 April 2024
Using public wifi is convenient, especially when you're out of the house and don't want to use your valuable data. However, logging in to a public network isn't as safe as surfing the internet at home.
Cybercriminals will often target public hotspots as a way of accessing devices with weak security measures.
Lets dive into how VPN technology can help protect you, so you can continue surfing on public Wi-Fi. weiterlesen...
7 April 2024
As the average online user browses through social media pages, does online shopping, or proceeds with distance learning at the university, the cybersecurity concerns are not that evident.
However, once a serious threat comes up, people usually appear totally helpless as they do not know how to deal with fraud or how to protect their privacy. It is only natural that when the talk goes about personal business or enterprise data leaks, it can become a serious issue. It is one of the reasons why people should consider at least basic cybersecurity training to become aware of their personal and workplace safety. weiterlesen...