3D printing has evolved into one of the best technologies of all time. What started out as a hobby has now become one of the efforts to mainstream the manufacturing process.
Today, 3D printing is aiding in various design processes, ranging from advanced medical products to agriculture and even aviation supplies. It also promises to create more cost-effective opportunities in all industries in the near future.
However, this does not mean 3D printing is the safest method. With all the glory, the technology is also attracting some cybersecurity nuisances, and knowing about them will likely make many progressing industries optimize their 3D printing processes more effectively.
The following are the critical cybersecurity challenges faced by 3D printing today.
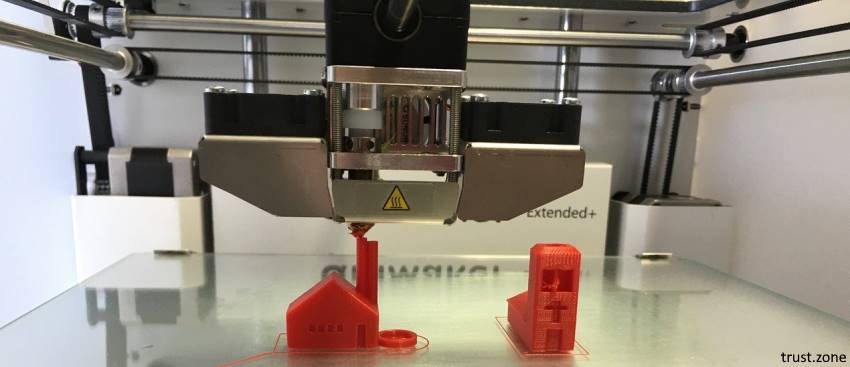
3D printing, also known as additive manufacturing, makes 3-dimensional solid objects from a digital design. These days, you can easily make pretty much everything into 3D with printing machines. However, this imposes a risk of counterfeit products for manufacturers.
You see, if someone gets access to a product’s design, they can easily print a counterfeit version. This way, the end-user will get a fake product and distribute the revenue entitled to the creator illegitimately.
Even worse, there is no guarantee that the second-party will use high-quality material to make the product. If they use inferior quality material, the production can cause your brand’s reputation to decline since the buyer wouldn’t know he is buying a counterfeit product.
It is also possible for data breaches to occur with 3D printing. For example, a medical device may contain personally identifiable information, and getting the device into the wrong hands can trigger privacy and security laws.
If someone who illegally intercepts a design discovers who they are meant for can sell the same to the black market or use it as a way to gain ransom.
The liability of any defect in the product lands on the manufacturer. This means that the manufacturer is responsible for any defects in the product. However, since 3D design services are connected through the internet, hackers can quickly gain access. And once they do, they can sneak design changes that can have an undesirable effect. The failure to produce a legitimate design can lead to damages that include deaths, property damage, litigation, and product recalls.
In the end, the manufacturer will have to bear the liability even if they weren’t actually responsible for the counterfeit product.
Traceability is another key concern facing the world of 3D printing. With regulations, requirements, and quality control coming into play, the need for traceability remains imperative in the world of 3D prints.
However, once the security of the process is compromised, the efficiency of the output is questioned. Did the printer receive the latest transmitted design? Was the right material used? These and many other questions will come into play about the authenticity of the product and the digital design.
As all other technological advancements, staying proactive remains the top priority to mitigate the risks involved in 3D printing. IT experts also recommend that every company relying on additive manufacturing should conduct a regular security assessment.
A comprehensive analysis will forewarn the manufacturers of the specific security risks involved and assess future potential threats more effectively.
In some industries, the manufacturers can take different measures such as using removable disc drives, disconnecting the additive manufacturing machine from the internet, adding windows firewalls, using a trustworthy VPN, and soundproofing can help lower the risk of cybercrime within the 3D environment.
Also, the manufacturers can do well by incorporating an encrypted design that will work in a way to allow only their printers to decrypt and design.
The product integrity issues are also on the mind of security experts working hard to develop a system that would help identify security threats. For example, a researching team from Georgia Tech and Rutgers University has developed a system that would help verify whether a 3D-printed object has been compromised or not. Their system works separately from corporate computer networks and assists in removing one of the major gateways to cybercrime.