Once you turn a computer on and connect it to anything, including your USB thumb drive, it is exposed to threats. Because of the nature of data movement methodologies and personal habits, there are threats everywhere. Know this and accept that fact and you have the right mindset to be safe. The Internet is a vast and cool place, but as with everything good, there is a counterculture who wants to exploit it for their motives. In a way, a healthy dose of paranoia is good when computers are involved. The first preventative is a password.
When your PC is on, someone can access your system if they want to and try hard enough. The only way to keep this from happening easily is to be defensive. Use passwords, and change them regularly. Make your password difficult to guess and harder to reproduce and decode. There are good tools to check whether or not your password is good enough.
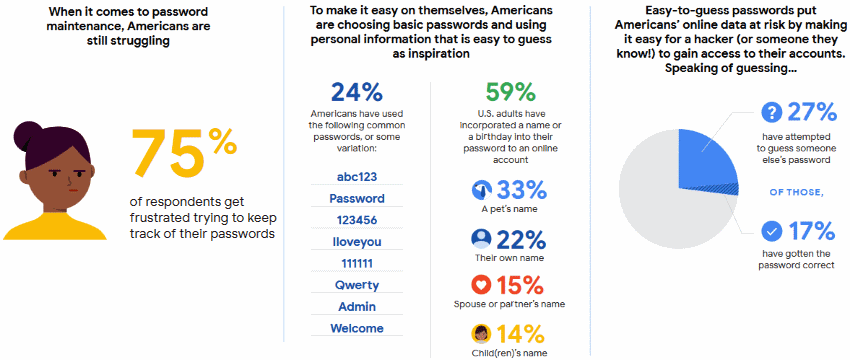
Did you know that 75% of Americans use weak passwords? We have decided to create a simple guide on how to make your password strong.
Be creative with passwords and combine words that aren’t found in common language. For example, the words, hot and snowstorm might become h0T$n_0w$torm. This incorporates some key elements in a good password. Here are some major tips:
You can make the password harder and more complex simply by adding more characters, numbers, or letters if you need more complexity. The password is just one thing you have under your control. Use it and change it often, as in monthly or every 90 days at a minimum. Not like the smoke detector batteries that get changed every six months. It is your data that is your electronic life, after all, how important is its security to you?
To be sure that your personal information particularly your location is under control, use a trustworthy VPN. In this case, you will be sure that nobody can get to know where you live or are at the moment or during the day. With a VPN your connection is encrypted and protected from prying eyes. Hackers can’t intercept your login and passwords, email and other personal details because your traffic is strongly encrypted.
Have your ever heard about tracking and status files at your PC? There are typically cookies (tiny text files) that allow the computer to visit a site without re-entering your email or password, your preferences or other information. They allow you to stay logged in to certain sites like your e-mail site. These files are automatically downloaded to the computer as you browse the Internet. You do have some control over them, but if you tighten down your acceptance of cookies, you are not allowed to visit certain sites. You have to choose your comfort level. These can be cleaned out periodically by setting the limit in your system as to how much space they can use.
Lastly, there is malicious software or malware, ransomware or trojans which gets on your computer. These are the most common cause of computer slowness, programs failing to function properly, and computer death as well as data loss. These are the files that piggyback on the cookies or attach themselves to e-mail or images which you unintentionally download along with a file. Yes, you did it, unintentionally, but you took some action which initiated a process, and the malware is on your system.
Fifteen years ago the virus was the most prevalent concern for computer systems. Today, it is ID theft through browser or computer hijacking. The only way to protect your computer is to be on the defensive – install antivirus software, enable firewall, back up your data regularly, update your software and use apps from trusted sources only.
Author Bio
Erica R. Gibson is a family lawyer. Besides, she is a legal writer at the service where everyone can ask to write an essay for me. She is highly interested in keeping up with advancing technologies. In this case, she spends her spare time reading various blogs to obtain new knowledge and improve her professional skills.