<< All posts1 July 2024
Did you know that Trust.Zone support the latest Military-Grade Encryption algorithm - AES-256 encryption?
AES256 is a symmetrical encryption algorithm. It is otherwise known as “military-grade encryption” because it is adopted by the U.S. and Canadian governments as standards for encrypting transited data and data at rest. Because of the 256-Bits length of the key and the number of hashes (14), it takes a long time for a hacker to perform a dictionary attack read more...
9 October 2023
If you want to have your employees’ trust and stay in line with regulations, there’s no doubt that employee data protection should be one of the most important tasks that your business can perform. But how can you ensure that employee data remains secure?
Leaving employees’ personal data unsecured means that your employees are at risk of identity theft, as well as other cybercrimes.
Fortunately, by using secure data storage methods such as VPNs, training your employees about cybersecurity, and reviewing access to data, you can make sure that employee data is as secure as possible.
Going into a future that will only become more dependent on data, ensuring that employee data is safe is a crucial step to guaranteeing that your organization is protected against cyberattacks. read more...
28 March 2023
Both an SSH and VPN are useful options for securing your data. We'll discuss how they differ, and which is the best choice for your business.
A recent report has shown that cyberattacks have risen by 38% the last year. Ensuring the integrity of data is becoming more and more of a challenge for companies; and one of the most important aspects of this is ensuring the security during data transfer.
Of course, security doesn’t just apply when you’re in the office. To stay safe, you need protection no matter where you or your employees are. But to ensure that, you’ll first need the right tools for protecting your data.
Let's look at two options that allow for safer data transfer: SSH and VPN. We’ll look at the difference between the two, and ask ‘which option is safer for your business?’. read more...
19 January 2023
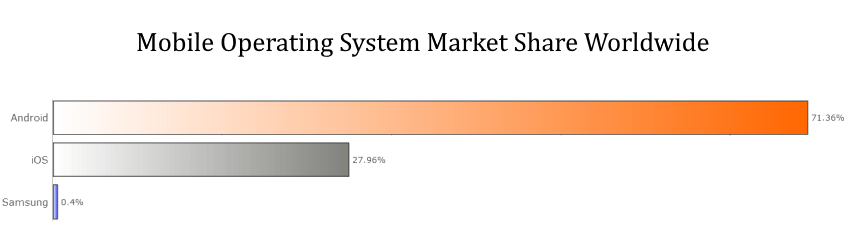
When you are looking to enhance the security of your personal smartphone the results can be very different depending on which operating system you are using.
Yes, because despite ever-improving technological advances that help to strengthen security, cyber criminals are also keeping up and attacking our data and networks in a myriad of novel and elaborate ways.
Therefore, if you want to stay ahead of the game, it’s time to review two of the most popular operating systems in the world and find out which one is the best and most secure, both for your personal data and for your business.
Who is the winner of the all-time OS security war — Apple or Android? Learn more in our comparative guide. read more...
11 January 2023
A data breach could cause your significant business losses. Are you aware that 84% of surveyed companies revealed they experienced over 2 data breaches in the last year?
It’s time to act and secure your cloud data. Are you ready to learn how?
Here are some main ways VPNs help secure cloud-based data and control access. read more...
21 December 2022
Businesses deal with a lot of confidential information daily. Whether it's customer data, financial reports, or trade secrets, companies must ensure that this information stays confidential.
One way to do this is by implementing best practices for securing confidential business information. These practices can help protect your data from unauthorized access, theft, or misuse. read more...
24 July 2022
While you may believe that your site doesn't have anything worth hacking, you'd be surprised how many websites are vulnerable to hacks.
Many website security breaches happen not to steal your data or mess with your layout. It uses your server as an email relay for spam and sets up a temporary server, which serves illegal files.
Another common way to abuse compromised machines is using a server as part of the botnet or mine for Bitcoins. Similarly, you can be hit by ransomware as well.
Hacking can be done by automated scripts that scour the internet to exploit a software’s known security problems. That’s why, in this post, we’ll talk about the eight practical tips on how you can keep your database safe and secure online: read more...
5 January 2022
It’s important to know that your property and belongings are safe at all times - and this includes your data and digital assets. One of the best ways to achieve this is to invest in a comprehensive cyber security set-up that you know you can trust.
Lets explore top 10 elements you should consider when making improvements to the cyber security systems that protect your home. read more...
3 January 2021
Website owners, especially those who have been doing business online for some time now, know all the trouble one hacker can make. Once these hackers gain access to your website they could do a lot of damage for your established business. This is why most businesses online hire a team of website security specialist just to make sure no one can access their sites without permission. read more...
1 January 2021
Concerned about website security? Do you think that your computer is susceptible to attacks by viruses, worms, and hackers?
You can never be certain that your computer is 100% safe and secure.
But there are steps that you can take to increase the security of your system, making it less susceptible to malicious programs. Given below are pointers and other information on how you can keep your computer safe from attacks by malicious programs. read more...