With cybercrime on the rise in recent years, companies are facing more cybersecurity issues than ever before.
As newer technologies take even more operations online, businesses are facing an increasing cybersecurity risk.
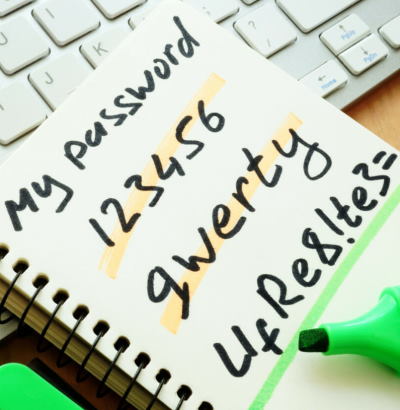
Where they used to be able to control their own networks and audit their own devices, many are now spread out over great distances and reliant on their employees’ password strength to keep their information secure.
In the midst of all this, author and technologist Bruce Sterling states “computer security needs a better solution than typing on a keyboard.” What’s the future of passwords, and are they still suitable for the digital world we find ourselves in?
 The tech industry has known for years that passwords are no longer secure on their own. Extra security measures like 2FA and Face ID have become essential parts of many high-security apps, like online banking, or even just to keep a major brand’s social media account secure.
The tech industry has known for years that passwords are no longer secure on their own. Extra security measures like 2FA and Face ID have become essential parts of many high-security apps, like online banking, or even just to keep a major brand’s social media account secure.
The fundamental weakness of most passwords makes these extra measures necessary. But the password is still an essential part of any signup process for sites.
While VPNs are becoming more commonly used as individuals become increasingly concerned about their own privacy, businesses often aren’t securing their remote workforces. With lots of remote workers working at coffee shops, libraries, or co-working spaces, they’re increasingly exposed to public wifi networks which have long been a target for hackers.
People have been questioning the use of passwords for a while, so why have they stuck around? What might ensure they stick around for longer?
Companies have stuck to passwords for so long because you can scale the use of them as much as you want for no time, money, or effort. If a company has to do even a quick security audit on all new hardware being used for the business, that’s a chunk of extra work if they hire multiple new employees. Also, if they’re paying for security software on a per-user basis, those costs go up every time they make a new hire.
These aren’t big problems for small-to-medium businesses, but a ‘blitzscaling’ startup can’t afford to have their IT teams occupied with this kind of work as the company grows.
While technologies such as biometrics - fingerprint recognition, Face ID, retina scanning - may be more secure than passwords, the average person would have concerns about that information being stored on a server.
In the future, 2FA will continue to become more common while getting stronger. Typically 2FA works by sending a one-time password (OTP) to your phone via text message. But hackers have since found a way around this.
The first high-profile victim of ‘SIM swapping’ was Twitter co-founder Jack Dorsey, whose Twitter account was taken over by hackers in 2019. In this method, the hackers are able to move your phone number over to their own device and receive your 2FA text messages, as easily as clicking the ‘Forgot Password?’ button.
One solution to this is that 2FAs are now delivered by a dedicated authenticator app.
A 2FA app reduces your ‘attack surface’ and makes your accounts safer. However unless it’s 2FA apps all the way down, you’re still securing this app with a regular password somewhere along the line.
Companies need that data to be private and accurate, and poor password strength on the part of anyone participant could make the whole thing vulnerable to cyberattacks. Among everything you need to know about blended learning as a teacher or an institution, one important factor is to make sure that your remote learning operation is secure.
These operations running across dozens of devices are the kind that needs extra protection. One compromised password could affect the whole group.
This is the reasoning behind calls for ‘passwordless’ security systems like biometrics, or other systems which identify you without a password.
While plenty of “passwordless” security features will be proposed in the coming years, recognizing people from their voice to the way they type, hackers will always find a way around them in time. When they do, they’ll have access to the faces, voices, and fingerprints on the server that was protected by a password.
Consumer-facing password managers have been around for a few years, but software providers are now catching on to the business need for the cheap, flexible, and easily-replaceable security that passwords provide.
With a team password manager, you’ve changed the ‘attack surface’ that hackers could use to target your company. While your passwords are safe on your own network and on remote employees’ devices, you now just have to worry about sending them securely.
While there are a number of ways you could do this, one of the easiest and most comprehensive solutions is a VPN that protects your company’s data as it moves between wifi networks. This prevents hackers from ‘listening in’ on your communications while you send passwords around. And it protects the rest of your data as teams work across the office, their homes, cafés, and co-working spaces around the world.
In conclusion, the way we handle cybersecurity is in urgent need of updating as we put more business online. Technologies like 2FA, biometrics, and password managers can provide some extra protection, and VPNs can protect sensitive data as it travels across an increasingly remote business world.
Author Bio:
Jessica Day is the Senior Director for Marketing Strategy at Dialpad, a modern cloud based call center solutions platform that takes every kind of conversation to the next level—turning conversations into opportunities. Jessica is an expert in collaborating with multifunctional teams to execute virtual call centers objectives and optimize marketing efforts, for both company and client campaigns. Here is her LinkedIn.